Modern cyber dangers are evolving swiftly, and routine scans are insufficient. In frequent vulnerability assessments and patch programs, vulnerability management discovers known problems. On the other hand, CPT simulates attacks in real time. Scans repair known issues, while pen tests verify that patched systems resist assault. While both have their own areas of issue resolving/addressing, let’s see how both are important pillar blocks of good cybersecurity measures.
According to studies, attackers have an average of 277 days between a vulnerability's emergence and its patch. Nearly 60% of breaches exploit known yet unpatched vulnerability. In other words, point-in-time repairs are insufficient. Businesses may drastically reduce vulnerability exploitability by combining vulnerability management and continuous testing. Only an ongoing plan can stay up.
What Actually is Vulnerability Management?
Vulnerability management finds, evaluates, and fixes security vulnerabilities in an organization's systems and applications. Approximately 82% of organizations prioritize vulnerabilities using structured prioritization (typically CVSS ratings) and 52% resolve serious concerns within a week.
In practice, a vulnerability assessment (VA) scan will unveil hidden weaknesses in your systems. It shows where patches or configuration modifications are needed. The severity and impact reports help IT teams fix the most hazardous holes first. After identifying risks, teams must determine whether to remedy, minimize, or accept them. Critical servers may be patched immediately, while low-risk, obsolete test devices may be retired. Tools track fixed and unfixed items during this cycle.
Why Vulnerability Management Alone Is Not Enough?
Despite good scanning, flaws creep through. Only tools and patches are covered by vulnerability management. It doesn't guarantee that fixes halt attacks or that no new flaws have arisen since the last scan. New code can expose vulnerabilities between scan cycles in dynamic systems (clouds, microservices, apps under development). Most companies wait months to fix high-risk issues, giving attackers time.
Vulnerability scanners don't examine how attackers chain vulnerabilities. They highlight potential issues but cannot confirm attack pathways or business-logic bugs. Data demonstrates that most breaches use many vulnerabilities or logic problems, not just one CVE. Human mistake and shifting agendas are issues. Scan lists are long and not all can be fixed promptly. Attackers jump on every gap, no matter how little. New vulnerabilities are also reported often.
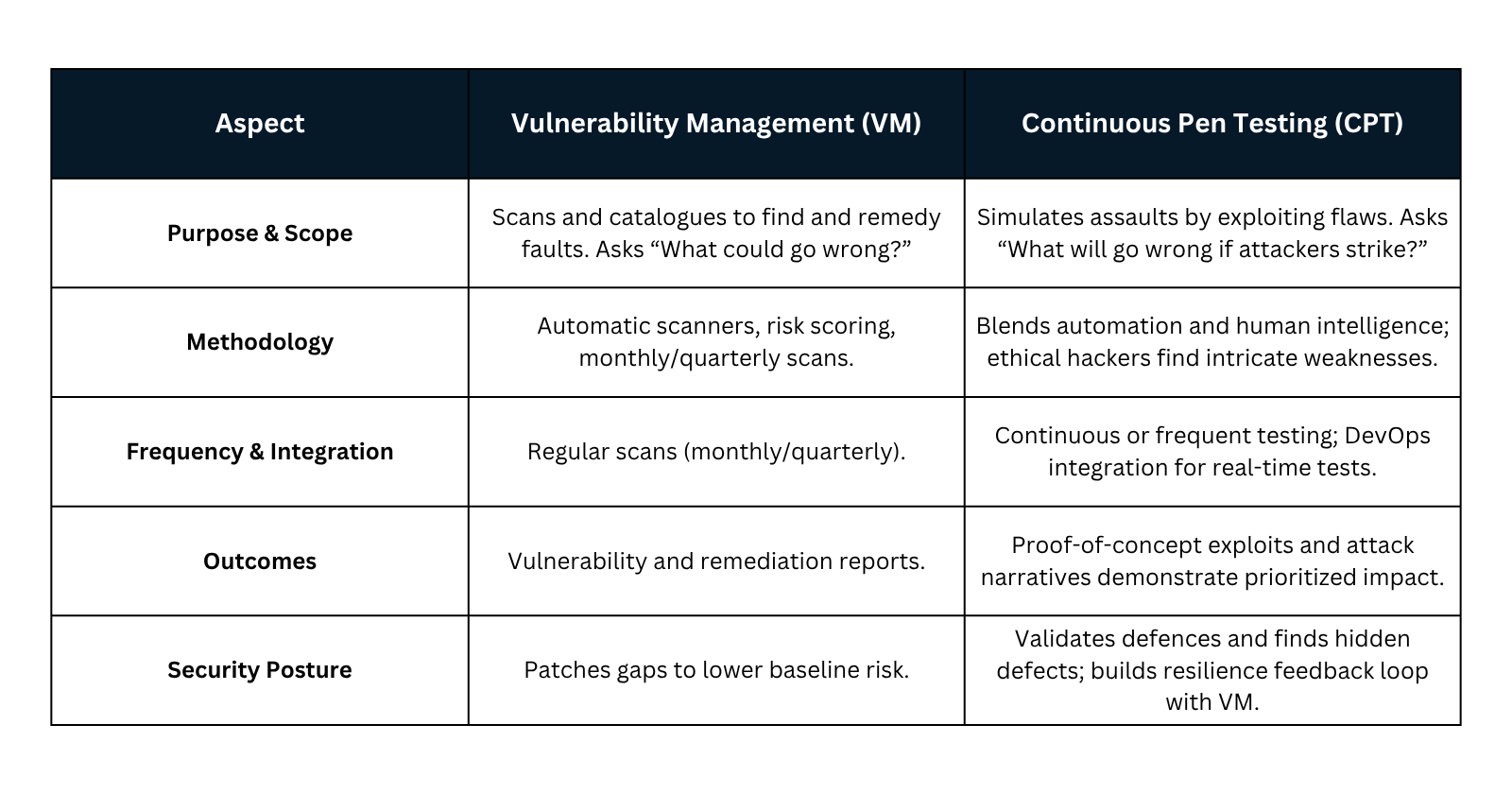
So, without verifying fixes and finding hidden hazards, a company is vulnerable. The table below contrasts the two approaches (details follow):
Vulnerability Management (VM) - Continuous scanning, patching, and prioritizing vulnerability lists for remediation.
Continuous Pen Testing (CPT) - Real-time attack simulation to test defenses by exploiting vulnerabilities.
How Continuous Pen Testing Works in Real Time?
Continuous Penetration Testing turns reactive into proactive. Instead of waiting months for the next pen test, security teams or service providers use automated tools and ethical hackers to constantly probe systems. This may entail scheduled scans on every new build or automated pen test suite against production apps.
CPT quickly finds vulnerabilities and checks patches. Tripwire claims that CPT helps companies find and fix issues quickly, decreasing the attacker's window. In other words, a CPT program would catch a new bug introduced by a software upgrade on the next automatic run, not months later.
Continuous testing has evident benefits. We find vulnerabilities faster and fix them before they become entrenched. This fast feedback loop closes gaps quickly.
Automatic scanning and manual verification are typical of continuous pen testing. Dashboards or DevOps pipelines display real-time results. CPT is connected with development and operations, so vulnerabilities may be fixed via CI/CD.
Major Differences - Vulnerability Management vs Continuous Pen Testing
The Risks of Relying Only on Vulnerability Management
Unpatched Vulnerabilities
Around 60% of breaches involve unpatched weaknesses. Attackers combine low-risk problems into large exploits. Average patching delay is ~277 days, resulting in extended exposure.
Delays Remediation
Scheduled fixes and batch scanning delay. Cyberattacks are growing and vulnerabilities may remain open for weeks.
Limited Scans
Tools detect known CVEs but overlook misconfigurations, logic errors, and exploit chains. Web app vulnerabilities account for 73% of breaches, often beyond scanner detection.
Compliance Gaps
PCI DSS requires active pen testing, not scans. Many companies must provide VAPT audit reports/certificates. VM alone might lead to fines or insurance denial.
Therefore, vulnerability management is crucial, but without regular testing, key defects and compliance holes remain exploitable.
Why Your Business Needs Both for Complete Cybersecurity?
The integration of vulnerability management and continuous penetration testing creates a comprehensive security framework that addresses the limitations of each individual approach. VAPT Company in India services that combine both methodologies provide organizations with broad vulnerability coverage and deep validation of actual security risks.
Organizations implementing both approaches report faster mean time to remediation (MTTR) and improved security metrics. The automation capabilities inherent in continuous testing platforms reduce the manual effort required for vulnerability validation while providing security teams with prioritized remediation guidance based on actual exploitability rather than theoretical risk scores.
Final Thoughts - Building Stronger Security with Continuous Testing
As the cybersecurity threats evolve, so must security testing methods. Identifying and tracking security vulnerabilities requires vulnerability management, but continuous penetration testing validates and prioritizes risk management in modern threat environments.
VAPT testing costs are decreasing due to automation and economies of scale, allowing enterprises of all sizes to perform enterprise-grade security testing. Success requires using both approaches as complimentary parts of a cybersecurity strategy rather than as competitors.
FAQs
1. What is the difference between VAPT Services and CPT?
VAPT Services detect vulnerabilities, while continuous penetration testing verifies whether they can be exploited.
2. How often should businesses undertake VAPT audits?
Traditional VAPT audit cycles are quarterly to annually, but continuous testing lets you examine modern threat dynamics.
3. What factors affect VAPT testing costs in India?
VAPT testing costs depend on organizational size, infrastructure complexity, assessment scope, and automated/manual testing methods.
4. Does VAPT certification require vulnerability management and penetration testing?
Many VAPT certification requirements involve systematic vulnerability identification and penetration testing to comply.
5. How do Indian VAPT Service Providers do continuous testing?
Leading VAPT Service Providers in India now offer hybrid vulnerability management with continuous monitoring and automated validation.
Write a comment ...